The Carrier IQ controversy exposed the long-festering problem of the Unique Device Identifiers (UDID), 40-digit-long strings of letters and numbers that distinguish one device from another. Most troubling, it cannot be blocked or removed by a user. (A report by the Electronic Freedom Foundation details how CIQ works.)
- Sent using Google Toolbar
Some Facts About Carrier IQ
There has been a rolling scandal about the Carrier IQ software installed by cell phone companies on 150 million phones, mostly within the United States. Subjects of outright disagreement have included the nature of the program, what information it actually collects, and under what circumstances. This post will attempt to explain Carrier IQ's architecture, and why apparently conflicting statements about it are in some instances simultaneously correct. The information in this post has been synthesised from sources including Trevor Eckhart, Ashkan Soltani, Dan Rosenberg, and Carrier IQ itself.
First, when people talk about "Carrier IQ," they can be referring to several different things. For clarity, I will give them each a number. You can think of senses 2, 3 and 4 as being "layers" of code that are wrapped around each other.
- The company, Carrier IQ, Inc.;
- a core software library that is written by Carrier IQ Inc. and which is present on all of the 150 million handsets;
- a Carrier IQ application or program running on a phone, which includes the software in layer 2, but also additional porting code written by handset manufacturers (sometimes called "original equipment manufacturers" or "OEMs"), mobile network operators ("telcos"), or baseband chipset manufacturers;
- the entire Carrier IQ stack, which includes the program described above as layer 3, but also often includes other code within a phone's Operating System and Baseband Processor OS to send data to layer 3. Like layer 3, this code is written by handset manufacturers, telcos or baseband manufacturers.1
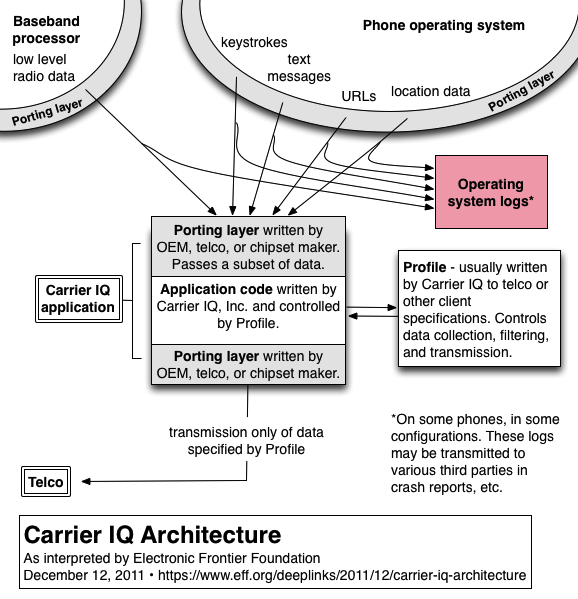
The huge amount of disagreement about various points, such as whether Carrier IQ logs keystrokes and text message content, is a result of using the term "Carrier IQ" to mean one of these four different things, as well as the fact that layers 3 and 4 vary on depending on which manufacturer built the phone, and which network it was customized for. Finally, there is an additional configuration file (called a "Profile") that controls the behavior of layer 2 and determines what information is actually sent from the phone to a carrier or other Carrier IQ client. Profiles are programs in a domain-specific filtering language; they are normally written by Carrier IQ Inc. to the specifications of a telco or other client.
There is consensus agreement that layers 2–4 collect information that can include location, browsing history (including HTTPS URLs), application use, battery use, and data about the phone's radio activity.2 The Carrier IQ Profile that is active on the phone determines where this information is intentionally transmitted, under what circumstances, the way in which it is filtered or processed beforehand, and whether it contains unique phone identifiers.
Our client Trevor Eckhart (whose research set off the present firestorm) and his subsequent collaborator Ashkan Soltani have shown that on some phones, dialer keypresses and SMS text are being written to system logs by layer 4 code. However, it seems that only much more limited types of keystroke and SMS information can make their way down from layer 4 into the underlying layer 2 Carrier IQ software.3 Unfortunately, our current belief is that the layer-4 logging that has been observed, which goes to Android system logs, is in fact being inadvertantly transmitted to some third parties and otherwise made available to other applications on the device.4 This happens when crash reporting tools collect copies of the system logs for debugging purposes. The recipients of such transmissions are unlikely to have anticipated receiving keystrokes, text messages, URLs or location information through such channels, but that can in fact happen on some of the phones to which Carrier IQ has been ported. What this means is that keystrokes, text message content and other very sensitive information is in fact being transmitted from some phones on which Carrier IQ is installed to third parties.
The complexities of this situation explain the apparent contradiction between claims by Carrier IQ Inc. and researchers examining code written by the company, who have said that the company does not collect full keystroke data or the content of text messages, and others who say that they have observed this happening. People on all sides of this debate may be simultaneously correct.
The information that we need now is a complete history of all of the Profiles that carriers have ever installed on their customers' phones, to learn what the carriers meant to collect. This would be a good place for regulators and others to start their inquiries. Separately, and equally importantly, the carriers and the OEMs need to take the steps necessary, whether OS updates or better yet, removing Carrier IQ software entirely, to stop the overbroad logging and transmittal of sensitive user data out of their customers' phones.
- 1. Carrier IQ Inc. provides reference code for telcos, handset and chipset manfuacturers implementing layers 3 and 4, which is sometimes used and sometimes not.
- 2. Carrier IQ calls these observable variables "metrics". The metrics are effectively an API that layers 3 and 4 use to make reports down to layer 2.
- 3. Eckhart and Soltani have demonstrated this on phones that run modified variants of the Android OS as customized by OEMs and telcos, but we should stress that Android as an OS is not to blame here. Android's relative openness has facilitated research on the situation, but the Carrier IQ stack has been ported to iPhones, BlackBerry devices, Symbian and Windows Mobile devices, and non-smartphones as well; we do not know what if any bugs exist in any of those ported versions of the stack.
- 4. The Android OS has a fine-grained permissions model in which any newly-installed software must disclose to the user that it may read copies of system logs before being installed. This is a good security design, but unfortunately, most users would not associate permissions to read system logs with permissions to read the sensitive information that some ports of the Carrier IQ stack are writing to the logs. Applications that come pre-installed on phones do not have the same install-time permissions dialog, but these apps at least sometimes use clickwrap dialogs. So we may face a situation where companies have taken some steps to try obtain consent from users for crash-reporting and debugging transmissions, without anybody being clear about how sensitive the data in those transmissions would end up being.
Thank You Jesus Christ for Creating The Way of Your Word!
WhatI I Love You Dearest Loving Lord Jesus Christ.
No comments:
Post a Comment